WebRTC standards provide a means for ensuring complete call security. When making calls over the public internet it is important to ensure that the call is secure or else someone other than the intended peer could easily eavesdrop on the call. It is even possible to alter the call if it is not properly secured. In order to provide complete call secrecy it is necessary to encrypt both the signaling and media channels.
Signaling
WebRTC provides security in the signaling channel using the WebSockets protocol over a Transport Layer Security (TLS) secured connection. This protocol begins by creating a secure TLS connection to a Hyper Text Transfer Protocol (HTTP) server and beginning the WebSocket handshake. During the TLS establishment the client will ask the server for its certificate which the client will then verify against a trusted Certificate Authority (CA). The CA’s pubic certificate will be able to verify if the server’s certificate was indeed signed by the CA’s private key. The CA’s signing of the server’s certificate indicates that the CA trusts the identity of the server and therefore the client can also trust them. This is referred to as the chain of trust. After the certificate verification takes place the client can be confident that the server is not an imposter trying to intercept the call and can continue with the establishment of a secure connection.
Media
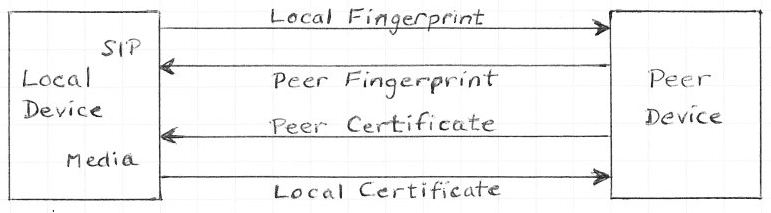
Security in the media layer is done using the Secure Real-time Transport Protocol (SRTP) which encrypts the media before sending it to the peer. WebRTC defines Datagram Transport Layer Security (DTLS) as a key establishment method for SRTP. DTLS has a similar handshake to that of TLS where peers send certificates to each other. As part of the DTLS-SRTP handshake the endpoints will send a cryptographic fingerprint of their certificates over the signaling layer that has already been secured. These fingerprints can be used along with the peer’s certificate to verify that the peer in the signaling layer is the same as the peer in the media layer. This ensures that there are no devices in the media layer attempting a man in the middle attack to eavesdrop on the media of the call. The combination of these security technologies ensures that the WebRTC call remains secure throughout every layer.

VOCAL’s solution is available for the above platforms. Please contact us for specific supported platforms.