The goal of cognitive radio networks (CRN) is to optimize the usage of spectrum resources. How can primary users and secondary users both use the network while maintaining Quality of Service (QoS) requirements? In the opportunistic spectrum access model, it is assumed that most radios are idle the majority of the time. Therefore, resources can be allocated to secondary users when the primary users are inactive. In the spectrum sharing model, this idle assumption is relaxed and techniques such as transmit beamforming can be used to spatially multiplex the spectrum to serve both primary and secondary users. By utilizing multi-antenna systems, the beampatterns of the antennas can be shaped to help prevent secondary users from interfering with the QoS of primary users, and visa versa.
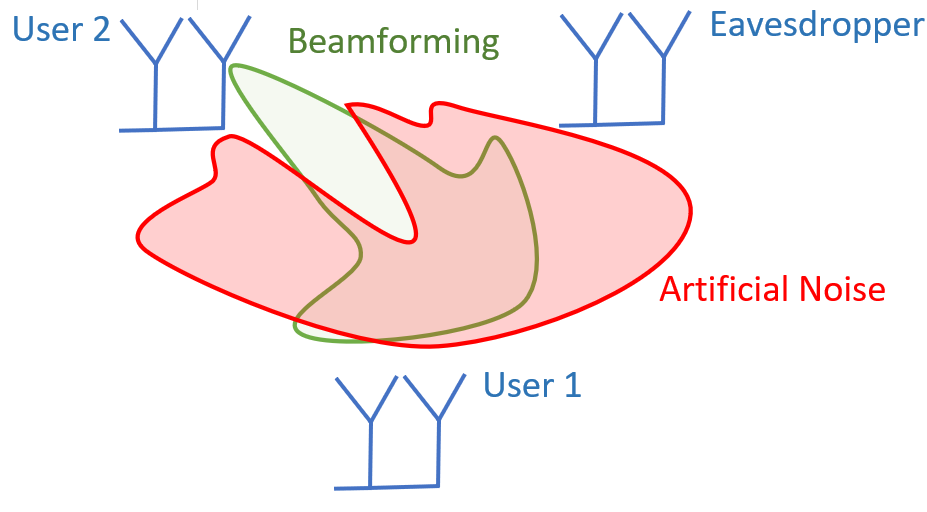
The utilization of multi-antenna systems in CRNs opens up another opportunity, Physical Layer Security (PLS). When the signal to noise ratio (SNR) of a desired communication target is higher than an eavesdropper, the communication is considered to have a secrecy capacity. By utilizing beamforming and artificial noise generation, a radiation pattern can be generated to maximize the secrecy capacity of the channel. This is referred to as Maximum Ratio Transmission. However, as previously discussed, in a spectrum sharing model, secondary users still need to be serviced with the proper QoS. By utilizing zero-forcing beamforming, nulls can be placed in the direction of the secondary user when the array is performing artificial noise generation.