Fax images may be sent using the ITU T.38 standard for real-time facsimile over the IP network. Unfortunately this gives criminals another method to encode and hide their nefarious communications. Lawful interception technologies give law enforcement and government agencies the ability to process and extract T.38 images from captured network data.
T.38 Image Extraction
During a T.38 fax transfer, data sent from a fax machine is collected by a T.38 gateway over the PSTN and sent across the IP network in T.38 packets to a remote T.38 gateway, which in turn sends the data to the intended destination fax machine. T.38 data can be transferred using TPKT over TCP, UDPTL over UDP, or RTP over UDP. By using the sequence numbers in each packet, along with any redundant or forward error correction (FEC) packets sent, the full T.38 stream can be reconstructed if the transmission was successful. Afterwards, the T.30 dialogue contained within the T.38 stream can be processed for fax image decoding to produce the image sent.
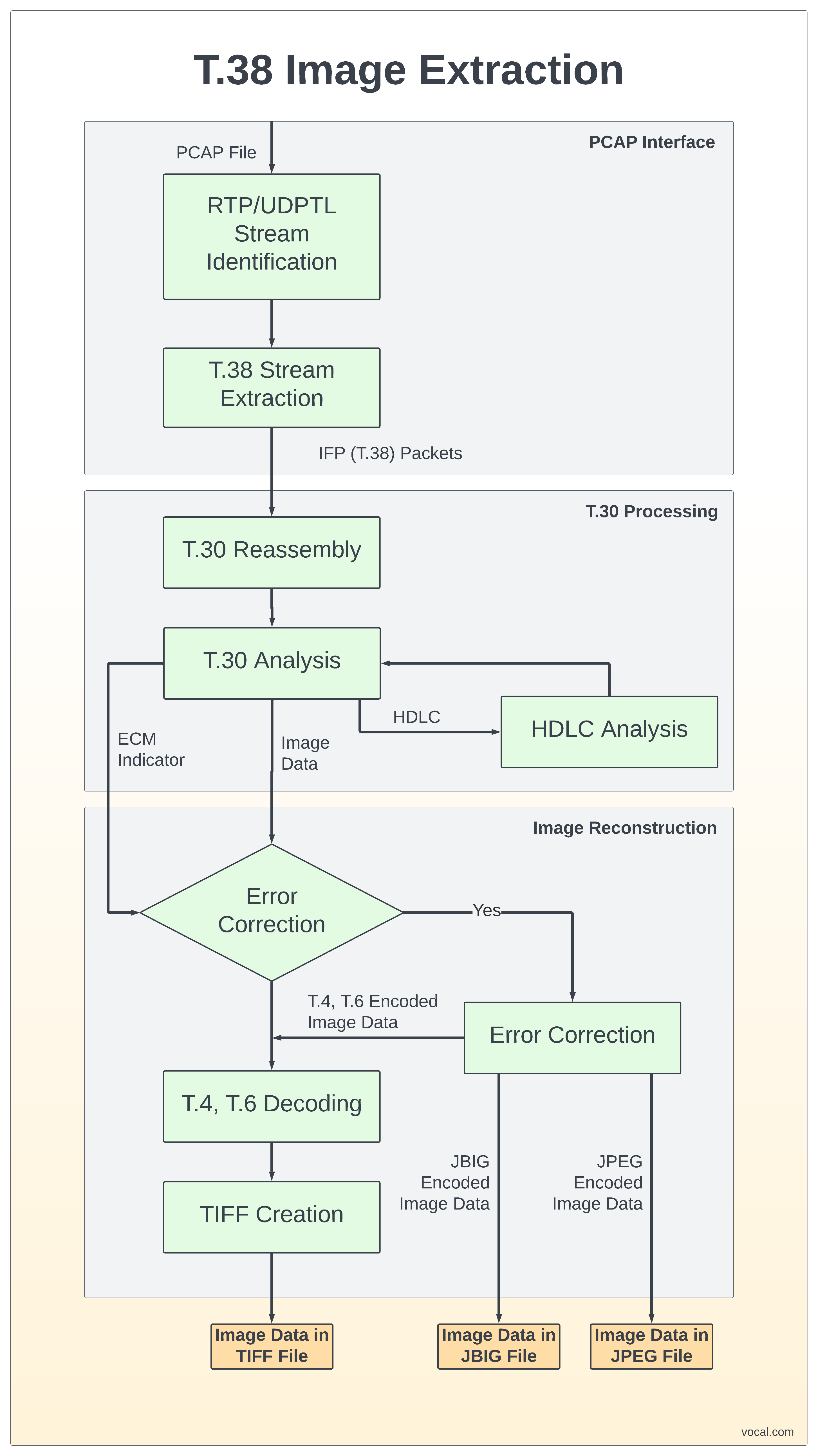
T.30 HDLC messages are sent over the IP network as one or more HDLC data frames followed with either an FCS OK or BAD frame, which indicates whether the T.30 HDLC frame is valid. HDLC data followed by an FCS BAD indication should be discarded. The T.30 DCS message, which contains the final negotiated parameters of the fax transmission, must be captured for fax image decoding to proceed. After the parameters have been negotiated, the modems are trained. If the training is successful, a T.30 CFR message is sent. After the CFR, the fax image data is transferred as either T.30 FCD messages as described above or as T.4 non-ECM data frames if Error Correction Mode (ECM) is not enabled. This data can be collected and assembled to form the T.4 or T.6 encoded image data, which can then be decoded using the knowledge gained from the T.30 DCS message.
Input Data Format
The T.38 Image Extraction Library accepts both file-based and packet-based input for high speed V.34 and group 3 fax image decoding. The file input is a libpcap capture file e.g., the output produced from a Wireshark trace. The capture file must contain the T.38 messages sent by both participants during the image transfer, and can contain any amount of non-T.38 traffic. These messages will be used to reconstruct the image transferred during the session. It is preferred that as much of the T.38 transmission as possible is provided in the capture file, as the absence of certain messages may result in failure to extract the image. When possible, partial output will be provided when the full image cannot be extracted. Support for other capture file formats can be provided on request.
In addition to capture files, the T.38 packets themselves can be input directly into the library, enabling real-time processing of T.38 streams. When using this approach, the user of the library is responsible for initializing and shutting down the T.38 processing.
Output Data Format
The output file format of the fax image decoder commonly will be either TIFF or the standard Microsoft bitmap format (bmp), and can be chosen for a specific implementation. Images are written in these formats and should be readable by nearly any image manipulation utility. Support for alternate page naming mechanisms is also available on request. For page image data, typically one output file is created per page, named in increasing numerical order and extracted from the recordings. A detailed logfile of each FAX session is also available from the fax demodulation software to assist in debug and analysis.
To summarize the extracted images, a short report file is produced that contains the following information: input file, source IP/port, destination IP/port, and for each page: width, length, resolution, ECM mode, modulation, compression.

VOCAL’s solution is available for the above platforms. Please contact us for specific supported platforms.